Digital Lifestyle
8 THINGS TO ASK YOUR SERVICE PROVIDER BEFORE YOU SUBSCRIBE
Do you know what you are signing up for when it comes to your mobile & internet subscriptions? Have you ever asked for details from your Service Provider? At the end of the month, you might suffer from paying your bill way too much than you expected due to the...
3G Sunset FAQ
1. What is 3G Sunset? As part of JENDELA or Jalinan Digital Negara, which is a comprehensive digital infrastructure plan aimed at addressing the arising needs and demand for better quality for fixed and mobile broadband coverage, amidst the COVID-19 pandemic and the...
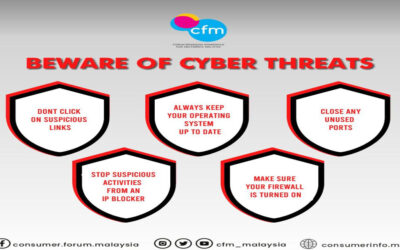
BEWARE OF CYBER THREATS! FOLLOW THESE 10 SAFETY TIPS
In every cyber activity we do there are various threats especially from ‘scammer’ or ‘hacker’ who will try their best to steal your personal information. As users we must be careful and always ensure that we are alert to the messages, emails we receive, and the...
6 CRITICAL THINGS YOU NEED TO DO FOR BETTER ONLINE SECURITY WHEN WORKING FROM HOME
Outdated software and firmware contain vulnerable loopholes that hackers can use to gain access to your systems. This holds true not only for your PC but for your home router and your smartphone too. While an office-managed IT network can handle such minutiae for you,...
THE ESSENTIAL SMART HOME PRIMER
Welcome to Smart Home technology. Learn the essential basics needed to build your dream Smart Home | CFM
FREEMIUM SOFTWARE. IS IT REALLY FREE?
FREEMIUM SOFTWARE. IS IT REALLY FREE? You have just encountered one of most popular business models for app developers. So buyer, beware…
SOCIAL MEDIA POLLING FOR BRANDS
Find out how you can harness the power of social media polling to get a leg up in your business | CFM #CFMmalaysia #SocialMediaLife
PROTECTING YOUR ONLINE PRIVACY AND PERSONAL DATA | CFM
To get started, here are a few crucial steps on protecting your online privacy and personal data. #ProtectYourDataPrivacy #CFMmalaysia
MAKE LIFE HAPPIER – BRIGHTEN UP AND DETOX YOUR SOCIAL MEDIA TIMELINE
Here are a few helpful sites to get you started: MAKE LIFE HAPPIER – BRIGHTEN UP AND DETOX YOUR SOCIAL MEDIA TIMELINE | CFM